
Early on in a cyberattack, adversaries concentrate on establishing a strong foothold within the target network in order to set the foundation for later, more sophisticated operations. Because it lays the groundwork for all later malevolent behaviors, this early phase is very important. An attacker’s first priorities after breaking into a network are to remain persistent, keep control, and learn more about the environment they have invaded.
In order to defend against sophisticated cyber threats, it is imperative to comprehend the strategies employed to acquire an initial advantage. Malicious network discovery activities can be quickly identified to halt an attack in its tracks and prevent it from getting worse. We will go further into these early-stage strategies in this blog and talk about how enterprises may strengthen their defenses to fend off such intrusions.
Gaining Access to a Network: The Initial Compromise
Getting initial access to the target network is a critical first step in any cyberattack. Attackers establish their foothold at this point, usually going unnoticed if their scheme is well-executed or if the organization has insufficient security measures in place. It is not necessary for the first compromised asset, known as “patient zero,” to be a Windows computer. In certain instances, the final phases of the assault might only affect a certain network section.
There are several techniques that attackers can use to gain initial access:
-
Exploiting Public-Facing Applications: Cybercriminals exploit weaknesses in public-facing applications such as web services and email hosts. These get work recognized flaws with free patches that corporations go to use or zero-day vulnerabilities that are obscure to software developers.
-
Phishing: Attackers utilize social engineering to deceive users into opening infected attachments, clicking on links, or disclosing sensitive information. This can be accomplished by email, social media, or other communication channels.
-
External Remote Services: Attackers target remote access services such as RDP VPN or VDI that are exposed to the internet without proper security measures like IP whitelisting or multi-factor validation.
-
Valid Accounts: Attackers compromise local, domain, or cloud accounts through brute-force attacks, password guessing, or stealing credentials from infected systems.
-
Drive-by Compromise: Attackers exploit vulnerabilities in user’s web browsers or steal application access tokens to gain unauthorized access.
-
Supply Chain Compromise: Attackers target software or hardware products used by potential victims, infecting them through the supply chain. Recent examples include the SolarWinds and Codecov attacks.
-
Trusted Relationship: Attackers exploit existing trust between individuals, networks, or systems to carry out malicious activities, making detection more difficult.
-
Replication through Removable Media: Attackers use USB drives or other removable media to deliver malware to target systems.
-
Hardware Additions: Attackers use computer accessories, networking hardware, or other devices to gain unauthorized access to a system or network.
Establishing a Foothold: The Crucial Steps After Initial Network Compromise
Once threat actors gain initial access to a target network, their next objective is to establish a strong and reliable foothold. This involves utilizing various tactics and techniques to maintain persistence, evade detection, escalate privileges, and access credentials. These tactics are all part of the MITRE ATT&CK® Enterprise Matrix and are crucial for a successful cyber attack.
Establishing a foothold is not a one-size-fits-all approach. Mature threat actors are well-versed in corporate environments and will tailor their methods depending on the initial access vector. Some common scenarios include:
- Remote access via RDP using a default local user account.
- Exploiting an unpatched vulnerability in Microsoft Exchange (e.g., ProxyNotShell) and dropping a web shell.
- Compromising a business application server used for testing purposes.
In each of these cases, the attackers will perform endpoint reconnaissance, gather information about the target system and its security posture, and then decide whether to persist on that particular host or escalate privileges.
To establish a foothold, attackers can employ a wide range of tactics and techniques. These include:
- External Remote Services (T1133)
- Create Account (T1136)
- Create or Modify System Process (T1543.003)
- Scheduled Task/Job: Scheduled Task (T1053.005)
- Boot or Logon Autostart Execution (T1547)
- Boot or Logon Initialization Scripts (T1037)
- Hijack Execution Flow (T1574)
- Modify Authentication Process (T1556) or Server Software Component (T1505)
- Event Triggered Execution: Component Object Model (COM) Hijacking (T1546.015)
- Event Triggered Execution: Windows Management Instrumentation Event Subscription (T1546.003)
Attackers can also use various techniques to escalate privileges, such as:
- Exploitation for Privilege Escalation (T1068): This includes exploiting operating system or software vulnerabilities to gain access to the SYSTEM user or higher privileges.
- Bypass User Account Control (T1548.002)
- Access Token Manipulation (T1134)
- Process Injection (T1631)
- Event Triggered Execution (T1546)
- Valid accounts (T1078): Once SYSTEM or local administrator access is obtained, attackers may utilize credential access techniques to gain domain-privileged accounts.
To gather authentication details and credentials, adversaries can use:
Defense evasion techniques are also crucial for attackers to continue their operations while avoiding detection. These tactics include:
- Impair Defenses (T1562)
- Indicator Removal (T1070)
- Hide Artifacts (T1564)
- File and Directory Permissions Modification (T1222)
- Masquerading (T1036)
- Hijack Execution Flow (T1574)
- Obfuscated Files or Information (T1027)
- Process Injection (T1055)
- Modifying Registry (T1112)
- Abuse Elevation Control Mechanism (T1548)
- Access Token Manipulation (T1134)
- BITS Jobs (T1197)
- Exploitation for Defense Evasion (T1211)
By employing these tactics and techniques, threat actors can effectively establish a foothold in a target network, paving the way for further stages of the attack, such as lateral movement and privilege escalation. It is essential for organizations to understand and defend against these techniques to mitigate the risk of successful cyber attacks.
Network Discovery: Unveiling the Network Layout and Active Directory Structure
After gaining initial access to a target network, attackers typically employ various tools and techniques to gather information about the network layout and Active Directory (AD) structure. The goal of network discovery is to understand the target environment better, identify potential targets, and plan the next steps of the attack.
Attackers often use built-in Windows tools, living-off-the-land utilities, or specialized reconnaissance tools to perform network discovery. Some common AD discovery tools include:
- ADRecon: A PowerShell-based tool for Active Directory reconnaissance
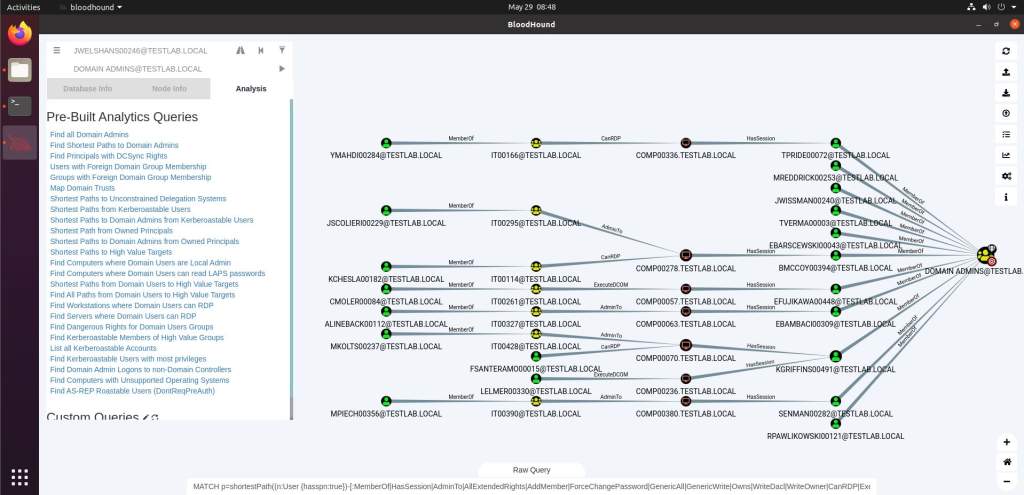
- BloodHound/SharpHound: Tools that use Windows API functions and LDAP to collect data from domain controllers and domain-joined Windows systems
- ADFind: A command-line Active Directory query tool
- ADExplorer: An advanced Active Directory viewer and editor from Sysinternals
- CrackMapExec: A Python-based post-exploitation tool
- PowerView: A tool for gaining network situational awareness
- LDAP Browser: Software for browsing and analyzing LDAP directories
Additionally, attackers may use built-in Windows tools such as:
- PowerShell built-in applets, like the ActiveDirectory module
- Nltest: A tool for performing network administrative tasks in the Active Directory domain
- Net.exe: A tool for controlling network interfaces, manipulating network shares, and monitoring user sessions and system services
Some tools, like BloodHound, provide a visual representation of relationships within the AD environment, making it easier for attackers to analyze and plan their next steps.
Attackers may also employ various network reconnaissance tools to map the network:
- SoftPerfect Network Scanner
- Advanced IP Scanner
- Advanced Port Scanner
- Nmap
- Zenmap
Windows built-in tools can also be used for network discovery:
- Net.exe
- Nbtscan
- Nmblookup
- Nslookup
- Ping
The information gathered during network discovery may include reachable subnets, hostname-to-IP address mapping, available ports, and potential unpatched systems. This information helps attackers maintain visibility and access across the target infrastructure and plan their next moves, such as privilege escalation, lateral movement, or deploying additional malware.
Attackers may also execute payloads within frameworks using in-memory execution techniques, like reflective DLL injection or shellcode-reflective DLL injection. This makes forensic analysis more challenging and requires user-space monitoring, such as Windows API function hooks.
The network discovery phase is crucial for attackers to understand the target environment, identify potential targets, and plan the subsequent steps of the attack. Detecting and disrupting this phase can significantly hinder an attacker’s ability to proceed with their malicious activities.







