The digital security landscape has witnessed the emergence of a new ransomware-as-a-service (RaaS) called Eldorado, targeting both Windows and Linux systems. This article explores the operational characteristics, targets, and implications of this threatening new player.
Table of Contents
About Eldorado Ransomware
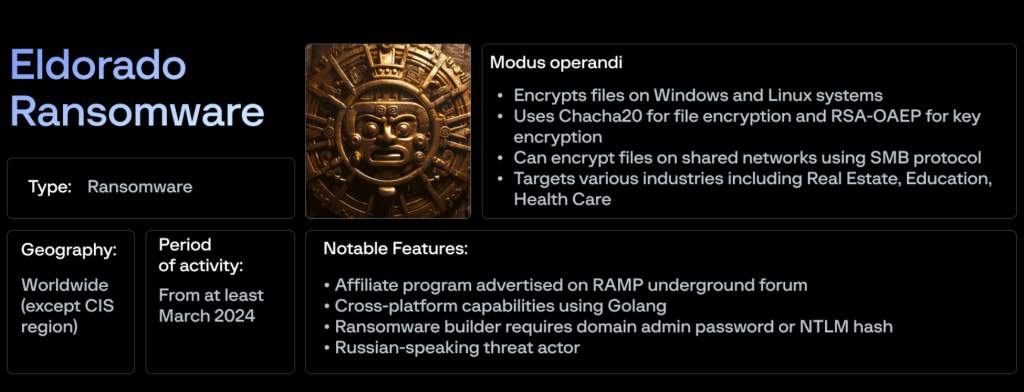
Eldorado was first spotted on March 16, 2024, through an advertisement on the ransomware forum RAMP. Group-IB, a cybersecurity firm based in Singapore, has analyzed the group’s activities, highlighting that the operation’s communications are predominantly in Russian and the malware differs significantly from known strains like LockBit or Babuk.
Encryption Capabilities and Variants
Leveraging Golang for its cross-platform functionality, Eldorado uses Chacha20 and RSA-OAEP to manage file and key encryption respectively. The ransomware is engineered to compromise files across networks via the SMB protocol and is available in four variations: esxi, esxi_64, win, and win_64.
Victims and Industries Affected
As of June 2024, Eldorado’s data leakage site lists 16 victims across various sectors including real estate, education, professional services, healthcare, and manufacturing. The majority of these victims are situated in the U.S., with others in Italy and Croatia.

Comparison with Other Ransomware Groups
Eldorado is among the emerging group of sophisticated ransomware operators engaging in double-extortion tactics, joining the likes of Arcus Media and LukaLocker. This approach typically involves not only encrypting the victim’s data but also threatening to release it publicly unless a ransom is paid. What sets LukaLocker apart in this category is its unique method of direct engagement with victims. Unlike most ransomware groups that rely on anonymous data leak sites to pressure their victims into paying ramsoms, LukaLocker takes a more direct approach. They initiate contact with their victims via telephone, making personal demands and negotiating the ransom.
Defensive Strategies and Recommendations
Organizations must prioritize establishing layered security measures, regular backup protocols, and comprehensive employee training to ward off ransomware attacks. Specific recommendations include:
- Deploying endpoint detection and response (EDR) systems
- Regularly updating and patching systems
- Segmenting networks to limit ransomware spread
- Conducting simulated phishing and ransomware attacks for preparedness
Future Outlook on Ransomware Threats
Eldorado exemplifies the ongoing innovation and perseverance of cybercriminal networks. The situational trends point toward frequent shifts in ransomware strategies, pushing cybersecurity professionals to continuously adapt and refine proactive measures and response strategies.
Conclusion
As ransomware techniques become more refined and decentralized through services like Eldorado, the implications for global cybersecurity are significant. Awareness, preparedness, and strategic responses will play pivotal roles in mitigating the impacts of these threats. This calls for a collaborative effort between organizations, cybersecurity experts, and law enforcement to tackle these evolving challenges head-on.







